Kraken is refusing to pay a criminal group that recruited employees, filmed internal support systems showing client data, and is now threatening to release the footage publicly.
The exchange’s chief security officer confirmed on April 14 that two separate insider incidents, the earliest dating to February 2025, are behind the extortion demand, and that roughly 2,000 accounts were exposed. No financial assets were at risk.
Kraken extortion linked to insider access
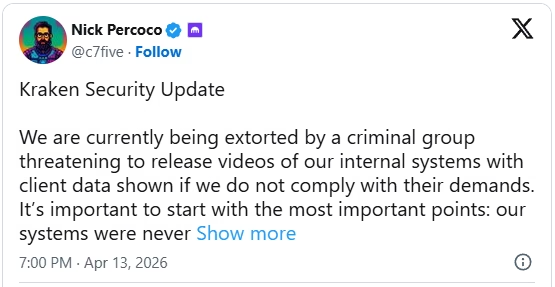
The Kraken extortion attempt stems from what the company describes as an insider threat involving two separate instances of unauthorized access to limited customer support data. According to Nick Percoco, the attackers are leveraging video evidence of internal systems to pressure the exchange into compliance.
“We are currently being extorted by a criminal group threatening to release videos of our internal systems with client data shown if we do not comply with their demands,” — Nick Percoco, Chief Security Officer, Kraken.
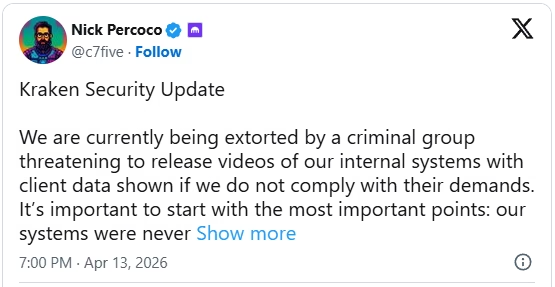
Percoco emphasized that despite the Kraken extortion attempt, the breach did not compromise financial systems or expose user funds. Instead, the incident was contained to internal support tools, accessed improperly by employees allegedly recruited by the attackers.
“It’s important to start with the most important points: our systems were never breached; funds were never at risk; we will not pay these criminals; we will not ever negotiate with bad actors,” — Nick Percoco, Chief Security Officer, Kraken.
Investigation reveals recruitment of employees
The origins of the Kraken extortion case trace back to February 2025, when the company received a tip about cybercriminals circulating a video that appeared to show access to its client support systems. This prompted an internal investigation, which uncovered that a support employee had been compromised or recruited by the threat actors.
More recently, another tip surfaced showing a newer video with similar insider access, reinforcing concerns about coordinated attempts behind the Kraken extortion effort.
In both instances, Kraken responded by revoking access, launching internal probes, and tightening its security protocols. The company also notified affected users directly where exposure was identified.
Despite the seriousness of the Kraken extortion attempt, the company maintains that only about 2,000 accounts were affected — representing roughly 0.02% of its global user base. The exposed data was limited to customer support information, not financial assets or login credentials.
Kraken refuses to negotiate with attackers
Kraken has taken a firm stance in response to the Kraken extortion attempt, making it clear that it will not engage with or pay the attackers. The company says it has gathered sufficient evidence to pursue legal action against those involved.
“We will not pay these criminals; we will not ever negotiate with bad actors,” — Nick Percoco, Chief Security Officer, Kraken.
The exchange is now working with federal law enforcement agencies across multiple jurisdictions to investigate the Kraken extortion case and bring those responsible to justice. This coordinated response reflects a growing trend among major firms refusing to yield to cyber extortion demands.
Insider threats pose growing crypto sector risk
The Kraken extortion incident highlights a broader and increasingly critical issue within the cryptocurrency industry: insider threats. Unlike traditional external hacks, these incidents exploit human vulnerabilities within organizations.
A comparable case emerged in mid-2025 when Coinbase suffered a major data breach after hackers bribed employees at a third-party support agency. That incident affected approximately 70,000 users and resulted in estimated damages of $400 million.
While the scale of the Kraken extortion case is significantly smaller, it underscores the persistent risk posed by malicious recruitment and internal compromise. As crypto platforms continue to expand globally, managing insider threats is becoming as crucial as defending against external attacks.