I covered the Drift exploit on April 1st, an incident that wiped nearly $296 million in user assets, based on on chain estimates and incident disclosures at the time. It felt like the kind of loss that forces an industry to pause.
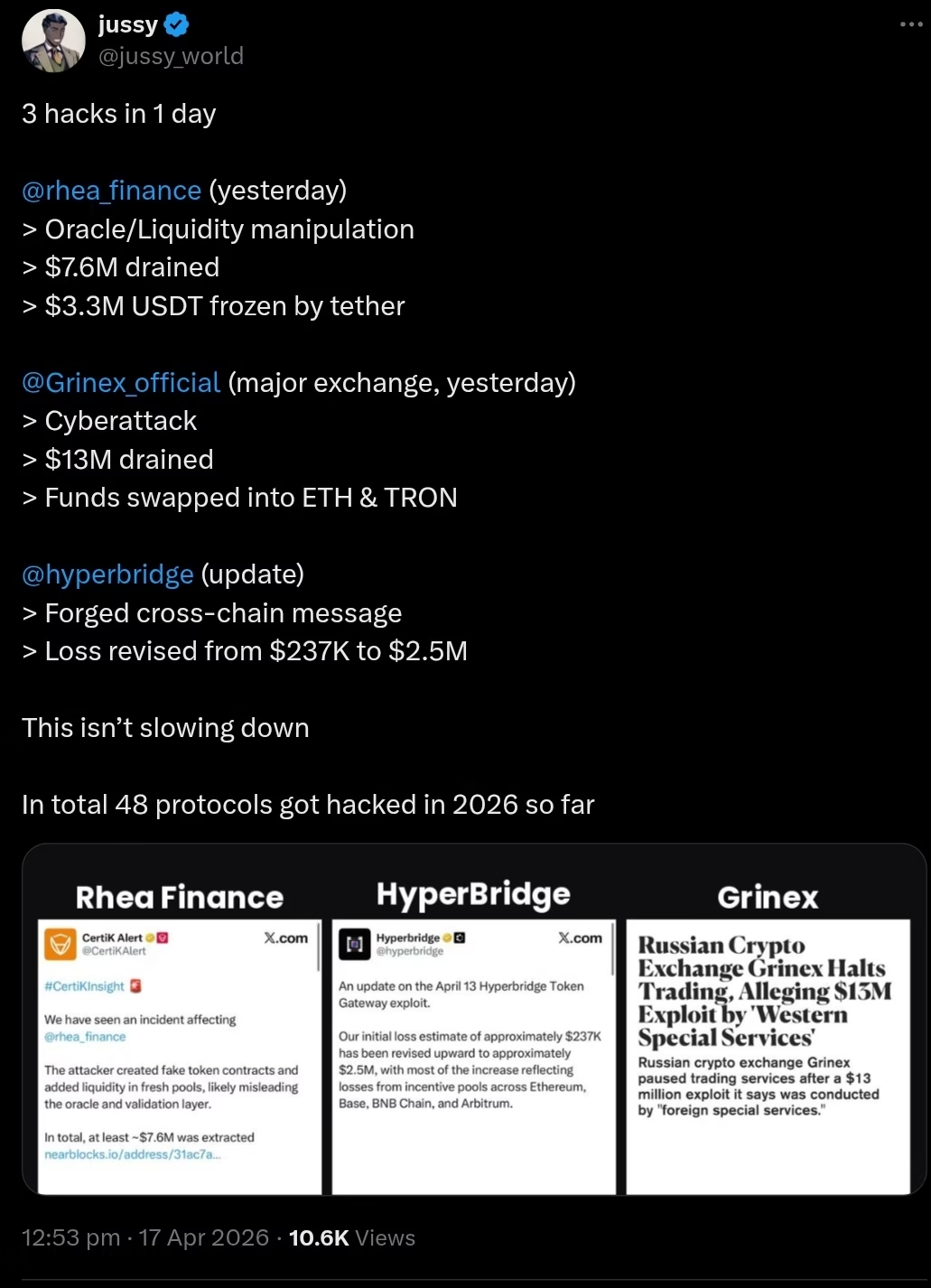
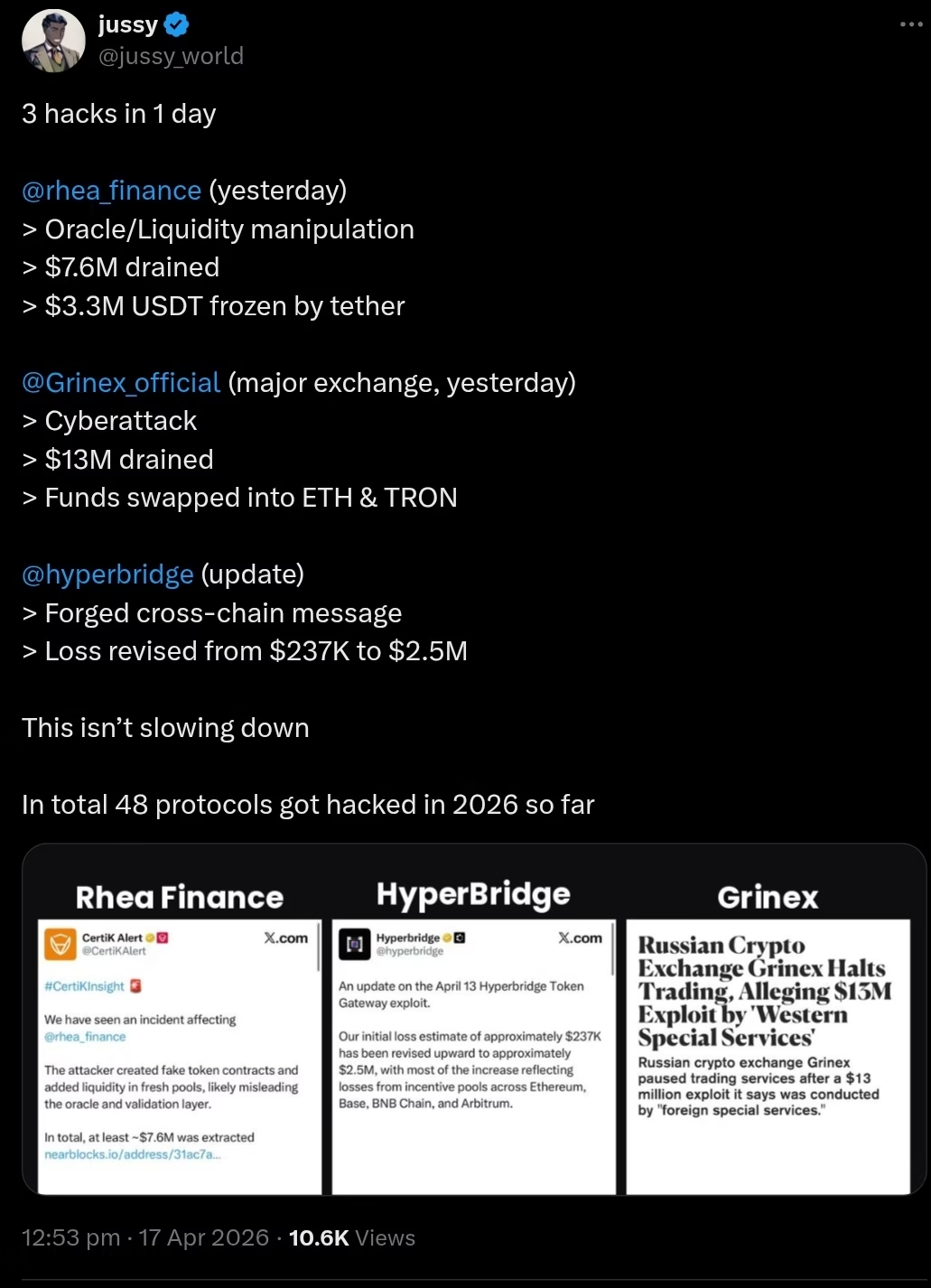
Two weeks later, we have had three more exploits in a single day.
April is not over, and aggregated losses for the month are already tracking past $300 million, according to early security dashboards and incident trackers. At some point, calling these events “incidents” starts to feel like calling a house fire a “thermal anomaly.”
The Same Exploits, Recycled
“Oracle manipulation. Forged cross chain messages. Hot wallet breaches. These are not zero days. They are known attack paths.”
On April 16, three separate failures hit three different parts of the crypto stack.
Rhea Finance, a major DeFi hub within the NEAR ecosystem, lost approximately $7.6 million after an attacker exploited oracle pricing mechanisms using low liquidity pools. This class of attack, manipulating price feeds via thin markets, has been documented repeatedly, from Harvest Finance in 2020 to Mango Markets in 2022.
Hyperbridge, a cross chain protocol connected to the Polkadot ecosystem, disclosed a Token Gateway exploit now estimated at roughly $2.5 million. Initial figures significantly underestimated the damage until cross chain reconciliation revealed activity across Ethereum, Base, BNB Chain, and Arbitrum.
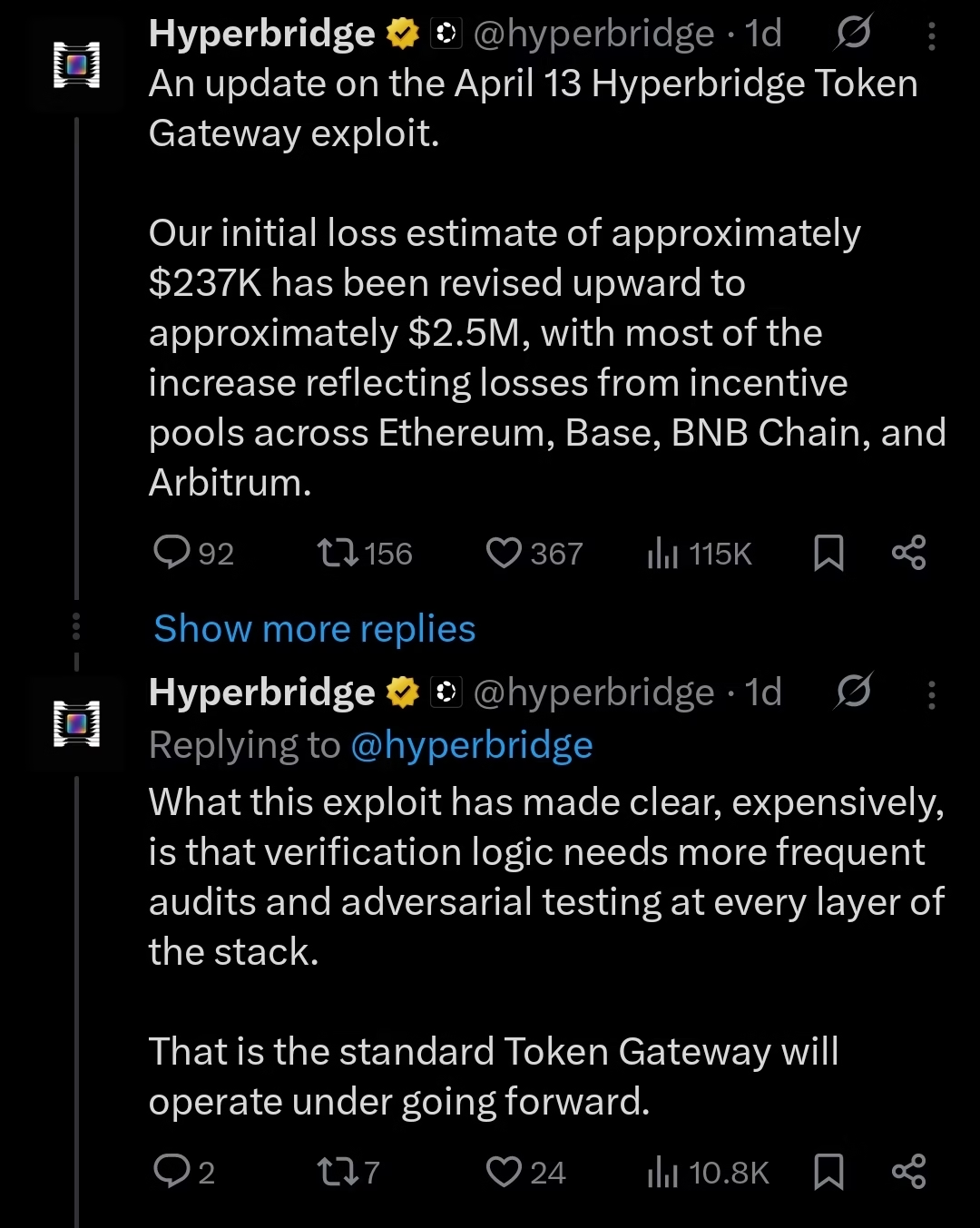
According to preliminary technical analysis, the attacker was able to bypass a critical proof verification mechanism, mint synthetic assets, and extract value through liquidity pools. The limiting factor was not security. It was insufficient liquidity to absorb the full exploit.
Then there is Grinex, a centralized exchange linked by investigators to the now sanctioned Garantex platform. Roughly $13 million was drained from hot wallets, with blockchain traces showing rapid conversion and dispersion of funds across multiple addresses. While the exchange attributed the breach to external actors, no verifiable public evidence has been presented to support that claim.
It is worth noting that Grinex is not DeFi. But its failure reflects the same underlying issue. Asset security is still treated as a secondary concern rather than core infrastructure.
Different systems. Same outcome.
The Post Mortem Loop
If you have followed this space long enough, you already know what comes next.
Each team will publish a detailed post mortem. The reports will identify the precise vulnerability, outline the exploit path, and propose fixes. The community will praise the transparency. Auditors will validate the findings. Patches will be deployed. Find Rhea Finance Incident Analysis and Community Disclosure here.

And somewhere else, a similar exploit will happen again.
Not because the industry lacks information, but because it lacks coordination and incentive alignment. Security knowledge in crypto is abundant. What is missing is consistent application across protocols, especially under pressure to ship quickly.
Hyperbridge’s case underscores a deeper cultural issue. Less than two weeks before the exploit, the team publicly joked about being unhackable.
 The timing is unfortunate, but the mindset is not uncommon. Security is still too often treated as a branding asset rather than an engineering discipline.
The timing is unfortunate, but the mindset is not uncommon. Security is still too often treated as a branding asset rather than an engineering discipline.
A Growing Attack Surface
According to blockchain security firm Hacken, over $482 million was lost across 44 incidents in Q1 2026 alone. That figure excludes the major April exploits now unfolding.
For context, 2025 closed with an estimated $3.4 billion in total crypto losses, based on aggregated industry reports.
These numbers are rising for a reason.
DeFi is not just growing. It is becoming more interconnected. Cross chain bridges, modular execution layers, and intent based systems are expanding what is possible. They are also expanding what can break.
Every new integration introduces new dependencies
- Oracles depend on market structure
- Bridges depend on verification logic
Protocols depend on assumptions about both
Hyperbridge processed hundreds of millions in cumulative volume prior to its exploit. That volume represents trust. Trust placed in systems that, in this case, failed under relatively familiar attack conditions.
The more composable the system becomes, the more a single failure can cascade across ecosystems.
Incentives Over Intentions
To be fair, there are signs of progress. Tether froze a portion of stolen funds linked to the Rhea exploit. Hyperbridge engaged compliance channels and publicly traced attacker flows. Affected protocols responded quickly to contain damage.
These are important responses. But they are reactive. Prevention is better than cure. The deeper issue is structural. Security competes directly with growth.
Stronger oracle systems require deeper liquidity assumptions and more robust validation layers. Safer bridge designs demand multi layer verification, redundancy, and slower execution. Cold storage reduces risk, but also reduces operational flexibility.
All of these improvements come at a cost
- Slower deployment
- Higher capital requirements
- Reduced user convenience
In a competitive environment, those trade offs are often deprioritized.
What Real Accountability Looks Like
If the industry is serious about reducing losses at scale, the standard needs to shift.
Not just better audits, but broader ones. Code reviews alone are not enough. Economic design and adversarial modeling need equal weight.
Not just decentralization, but redundancy. Critical systems like oracles and bridges cannot rely on single points of failure, whether technical or economic.
Not just transparency, but preemption. Publishing post mortems is valuable, but preventing repeat exploits across protocols is what actually moves the needle.
None of this is theoretical. These are known best practices, just unevenly applied.
The Cost Is Not Abstract
Behind every exploit are real users.
Wallets frozen. Funds inaccessible. Positions liquidated. In some cases, life savings erased.
Rhea users saw a core DeFi protocol halt operations after manipulated inputs compromised its lending logic. Hyperbridge users now face uncertain compensation timelines tied to token distributions. Grinex users are left navigating the fallout of a breach with limited clarity and accountability.
The Industry’s Defining Choice
Sixteen days into April, and losses have already crossed hundreds of millions of dollars. The trajectory is clear. More capital, more complexity, more risk.The question now is not whether exploits will continue.It will. It is whether the industry is willing to treat security as a product layer, something designed, funded, and continuously improved, or continue treating it as a reactive function.
Because right now, the gap is not in knowledge. It is in priorities. And until that changes, the pattern will hold.











 The timing is unfortunate, but the mindset is not uncommon. Security is still too often treated as a branding asset rather than an engineering discipline.
The timing is unfortunate, but the mindset is not uncommon. Security is still too often treated as a branding asset rather than an engineering discipline.