On April 18, 2026, a compromised peer contract on Unichain allowed the release of unbacked rsETH through LayerZero. The attacker deposited that synthetic collateral on Aave V3 and borrowed over 82,600 ETH roughly $195 million before the market could respond. Potential bad debt on Aave now sits between $177 million and $290 million. Aave froze its rsETH markets. Kelp DAO halted contracts. Dozens of protocols paused related activity.
Then the exits began.
Aave’s TVL dropped from $26.4 billion to $20.1 billion in hours. MEXC withdrew $431 million. A wallet linked to Nonco pulled $405.7 million. Abraxas Capital pulled $392 million. When the largest lenders in DeFi flee a protocol at that velocity, it is not panic. It is a verdict.
Two days earlier, I wrote that crypto had lost $23 million in a single day to attacks it already knew how to prevent oracle manipulation on Rhea Finance, a proof verification failure on Hyperbridge, a hot wallet breach on Grinex. At the time, April’s losses were approaching $300 million. They are now past $600 million, with eleven days left in the month.
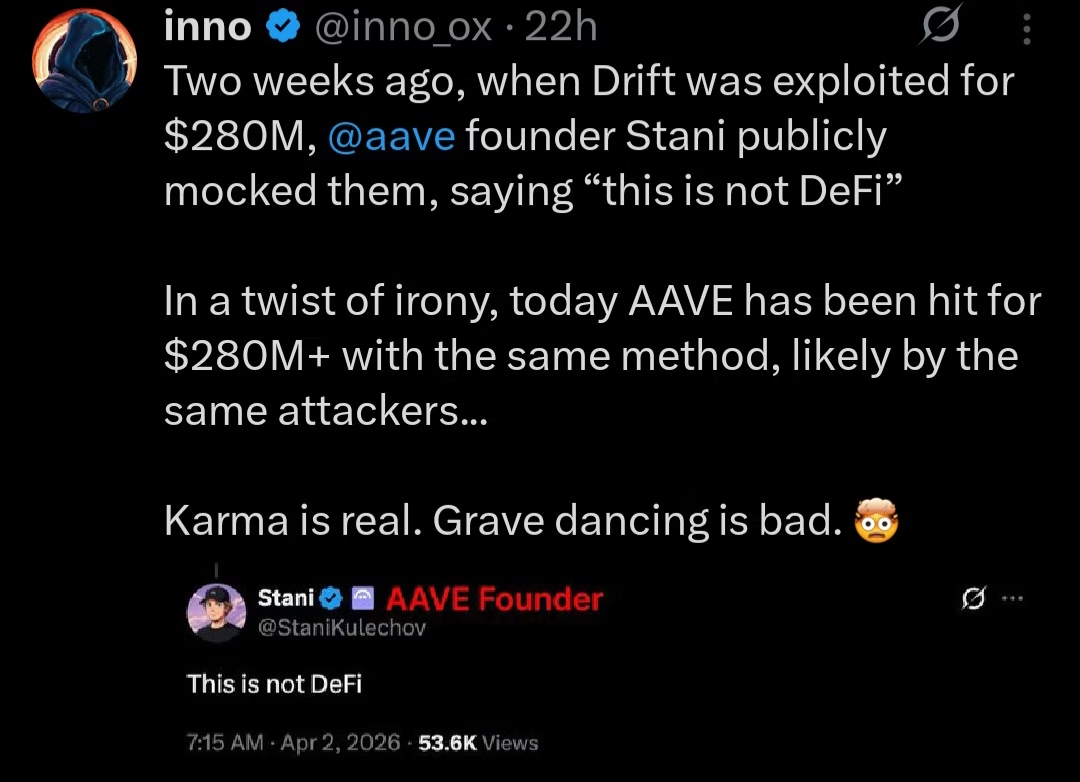
Grave Dancing Has a Price
The Aave-Drift dynamic deserves more than a footnote. When Drift Protocol was exploited two weeks ago, Kulechov’s public response framing the failure as evidence that Drift was “not DeFi” was widely circulated. The implication was architectural superiority. The unstated claim was that Aave had solved the problems Drift had not.
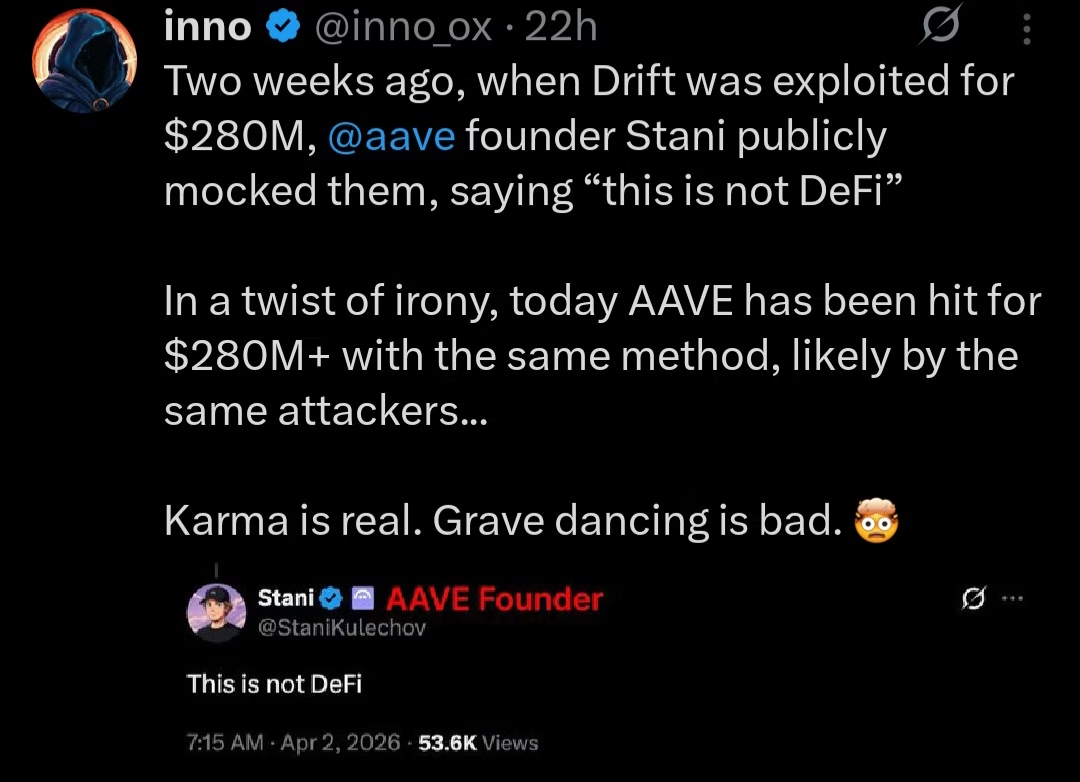
On April 18, Aave’s rsETH markets became the vehicle for the largest single exploit of 2026. The method: a cross-chain trust failure allowing synthetic collateral to be minted and deposited as if it were real. The same class of attack. Possibly the same attackers.
This is not a story about karma, though the timing is difficult to ignore. It is a story about what happens when security discourse becomes competitive positioning. When protocol founders treat rivals’ failures as marketing opportunities, they reveal something important: that the public performance of rigor and the private practice of it are not always the same thing.
Aave’s contracts were not directly exploited that much is technically accurate. But Aave had deep, unguarded exposure to rsETH collateral on the assumption that Kelp DAO’s bridge had robust peer verification. That assumption was wrong. The bad debt is real.
The Composability Tax
Cross-chain infrastructure is now the most dangerous surface in DeFi not because it is poorly understood, but because the incentives to secure it properly compete directly with the incentives to ship it fast and integrate it widely. Kelp DAO’s rsETH had deep integrations across Aave, Unichain, and LayerZero before April 18. That breadth was its value proposition. It was also what made the exploit so systemically damaging.
The attacker did not just hit Kelp DAO. They hit everything Kelp DAO touched. Every integration is a trust dependency. Every trust dependency is an attack surface. As DeFi becomes more composable cross-chain collateral, modular execution layers, intent-based systems the attack surface expands faster than the security tooling built to contain it.
Hyperbridge, exploited two days earlier for $2.5 million, had processed hundreds of millions in cumulative volume before its proof verification mechanism failed. The volume was evidence of trust. The trust was not fully warranted.
The pattern holds across the April incidents: Rhea Finance’s oracle manipulation relied on assumptions about liquidity depth that a patient attacker could violate. Hyperbridge’s bridge security relied on verification logic that could be bypassed.
Kelp DAO’s peer trust model relied on contract integrity that was compromised. In each case, the integration worked until it didn’t and when it didn’t, the blast radius extended far beyond the protocol itself.
This is the composability tax. You pay it not when you integrate, but when the thing you integrated with fails. And right now, the industry is paying it at scale. Q1 2026 produced $482 million in losses across 44 incidents, according to Hacken. April alone has already exceeded that figure. The annual trajectory is running well past 2025’s estimated $3.4 billion total. These are not anomalies. They are the compounding interest on deferred security investment.
What a Billionaire’s Tweet Tells You
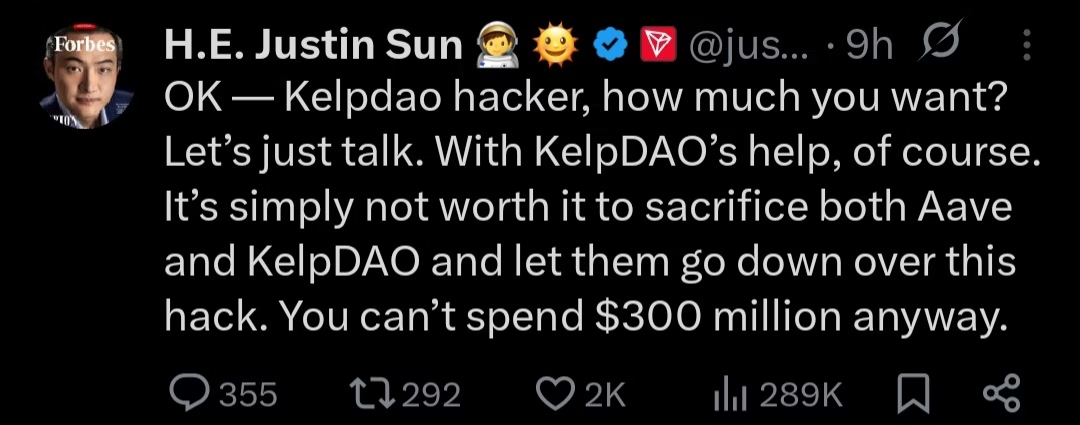
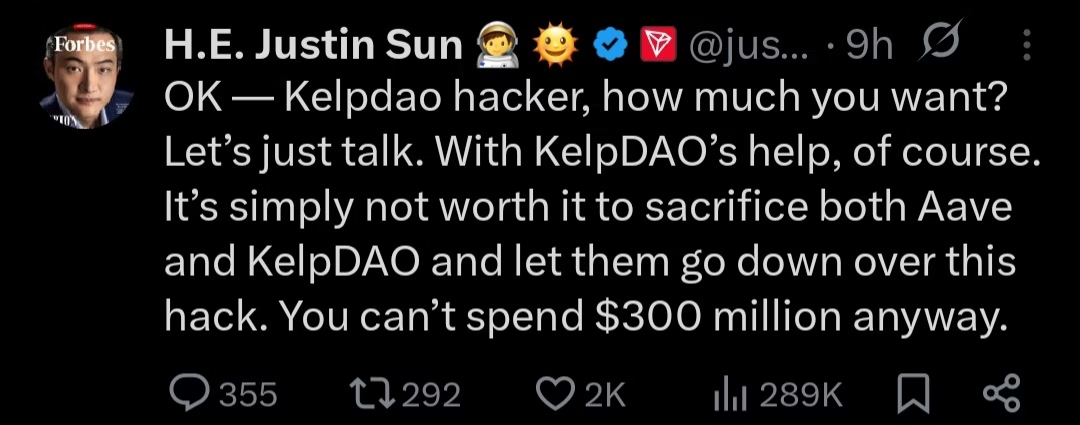
Justin Sun‘s public appeal to the KelpDAO attacker broadcast on X, framing the $290 million as money the hacker “can’t spend anyway” and proposing a direct negotiation with Kelp DAO’s help is easy to read as spectacle. It should be read as data.
It tells you what enforcement actually looks like in practice. Chain analytics can trace funds. Compliance channels can flag addresses. Tether can freeze USDT reserves in specific cases and in at least one instance, has gone further by leading the $150 million recovery plan for Drift Protocol, stabilising its relaunch and deepening USD₮ integration on Solana in the process thus suggesting that the largest stablecoin issuer in the world sees strategic value in being the infrastructure that catches protocols when they fall not just the rails they run on.
In this case, Sun’s might be wanting a situation where the attacker returns a portion of what they took and keeps the rest as an implicit fee for identifying the vulnerability.
This looks more like a settlement process that prices the breach as a service than security.
Sun’s framing; “it’s simply not worth it to sacrifice both Aave and KelpDAO over this” reflects a genuine calculation. The alternative to negotiation is watching bad debt crystallise and confidence collapse further.
In that context, paying a fraction of the stolen funds to stabilise the ecosystem is rational triage. But rational triage is not the same as deterrence. And an industry whose primary enforcement mechanism is asking attackers nicely to give some of it back is not an industry that has solved its security problem.
What Would Actually Move the Needle
The gap is not technical. Every post mortem from the April exploits will correctly identify the vulnerability, propose a fix, and recommend broader adoption of the relevant safeguard. The community will praise the transparency. The fix will be deployed. And somewhere else in the stack, a structurally similar failure will occur because the knowledge exists but the incentives to apply it consistently do not.
Protocols compete for TVL. TVL grows through integrations. Integrations require speed. A bridge that takes eight months to fully verify its peer trust model ships behind competitors who take four. Users flow to what is live and liquid. Until the cost of a breach to founders, to investors, to token holders consistently exceeds the competitive cost of building slowly, that calculus will not change.
What moves incentives is not transparency. It is pricing. Insurance markets that accurately price protocol risk based on audited cross-chain dependencies. Institutional capital that demands verified bridge security as a condition of deployment.
Regulatory frameworks that treat verification failures in cross-chain infrastructure with the same seriousness as custodial fraud in centralised systems. None of these mechanisms are fully in place. All of them are more likely to produce consistent security investment than another cycle of post mortems and community praise.
Aave’s response to the crisis was measured and technically sound. The freeze was appropriate. The commitment to explore deficit offsets if bad debt is confirmed is responsible.
But measured crisis communication is downstream of the decision to accept rsETH as collateral without fully stress-testing the bridge assumption it rested on. That decision was made in a competitive environment that rewards integration speed. Changing the outcome requires changing the environment.
The Cost Is Not Abstract
Behind the $6.28 billion TVL flight from Aave are real positions. Behind the Kelp DAO users now waiting on uncertain compensation timelines tied to token distributions are real people who trusted the infrastructure to hold. Behind every protocol that paused rsETH activity on April 18 are teams doing damage assessment on integrations they built in good faith.
Sixteen days into April, crypto losses for the month have already crossed $600 million. The month is not over. The year is not over. The composability of DeFi will continue to grow, and with it the potential blast radius of every unverified trust assumption embedded in a bridge, an oracle, or a peer contract.
The industry is not short on knowledge. It publishes detailed post mortems. It runs bug bounty programmes. It funds security research. It knows what oracle manipulation looks like. It knows what proof verification failures look like. It knew, before April 18, what a compromised peer contract on a cross-chain bridge could do.
What it has not yet decided collectively, structurally, in the way that actually changes incentives is whether security is a product layer or a reaction function.
Until it does, the number at the top of next month’s damage report will be larger than this one.